- June 30 2025
- Alejandro Rizzo
- April 22 2025
- Codacy
Codacy Guardrails: Free Real Time Enforcement of Security and Quality Standards
READ MORE
- April 15 2025
- Codacy
Codacy DAST: Scan Your Running Applications for Security Vulnerabilities
READ MORE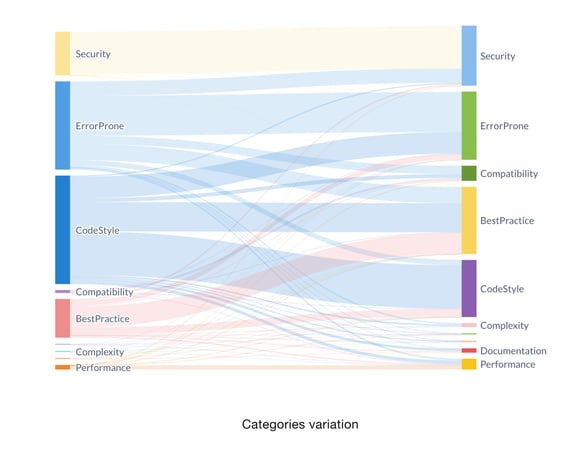
30/06/2025
At Codacy, we integrate 34 open-source tools to provide insights into code quality and security across 43 different programming languages. Many of...
08/05/2025
"Imagine vibe-coding in your favorite LLM, without the vibe migraine."
08/05/2025
AI tools are changing the game for developers. Whether you're using them to autocomplete code, generate new code, debug issues, or even streamline your...

22/04/2025
Last week, we unveiled Codacy Guardrails and its first small “hello world” moment: an MCP server that can connect with Codacy security and quality data...

15/04/2025
We’re excited to announce the early access release of Dynamic Application Security Testing (DAST) for Codacy!

08/04/2025
We are excited to share that Lizard, Codacy's recently integrated tool for detecting and reporting code complexity issues, has been enhanced and now...
Subscribe
to our blog
Stay updated with our monthly newsletter.
.svg)



